Donations!
According to Sourceforge.Net, the MSN Shadow was downloaded more than 32.000 times, showing that several people have liked the software.
So, to support my additional work on this project like a version for Windows, capture of file transfers and others improvements, I would like to ask for some donation if you can.
I would not like to stop providing this software in open source format, but I can not work for nothing!
If you need a better software, more complete, running in more platforms, make a donation and I will work hard for that. Thanks for your time!
Thanks for your time!
Gabriel
MSN Shadow new version
New version of the MSN Shadow Forensics Tool.
New features added:
-- Auto detection of video traffic
-- Capture of contact lists
-- Reading of PCAP files
-- New colors!
The version 0.3 can be downloaded in http://sourceforge.net/projects/msnshadow
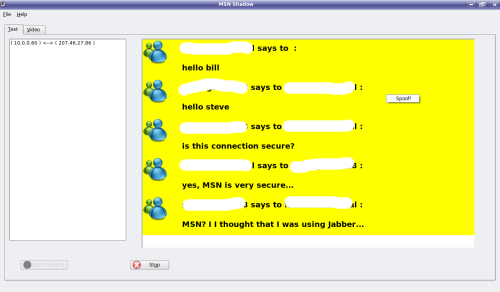
MSN Shadow Beta Version (MSN FORENSICS)
MSN Shadow beta version is a forensics tool for analysis and digital investigation for the MSN protocol.
This tool can perform several active investigation techniques in Microsoft Notification Protocol.
It has features such as:
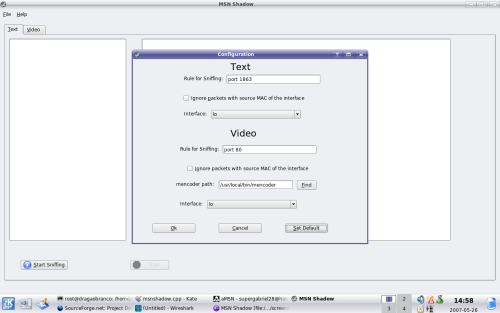
-- MSN text sniffing
-- MSN video sniffing
-- Spoofing messages
-- Hijacking Sessions
-- Shutdown users
-- Save text sniffed in HTML format
-- Save video sniffed in AVI format
This software depends on QT, libmimic (farsight.sourceforge.net) and libpcap.
Contact: gabrielmn at users.sourceforge.net
Download: http://sourceforge.net/projects/msnshadow
What is MSN Shadow?
What is MSN Shadow?
MSN Shadow is a forensics tool developed to demonstrate several security proofs of concept in the MSN protocol.
Is it possible to spoof MSN?
Yes...
The tool will save the sequence number and ack number of every connection sniffed. When the user spoof one of the sides of the connection, this numbers will be used and the software will send a RST packet.
With the RST packet the connection will close. In free software clients like Kopete and aMSN, it will appear a message informing that. But in official clients, this situation will not be perceived. This packet is necessary because the spoofing will change the sequence number of the side and the synchronism will be wronged.
The spoofing mechanism can be improved and I'm working for it! But, for now, it works.
The Hijack test will do the same thing of the spoofing, but it will do two iptables rules, hindering the packets from one side to achieve another(considering you are doing a arpspoof or a dos attack of one side). And a new window will appear allowing you to continue the conversation as you were the hijacked person.
The kick user command will send a RST packet to connection of the selected user with the server. This connection will be find out selecting special packets sent only by the server.
How do you sniff video?
Video is just binary code inside the packet. The only thing it needs is the decoder process.
Like Kopete or aMSN, MSN Shadow uses libmimic API[1] for decode video packets and show them to the user. To save the video, is necessary the 'mencoder' software, which can be downloaded from MPlayer site[2].
For technical information, I initializes de decoder init function of the libmimic API with a frame key video of a webcam connection which I sniffed.
Who did make this tool?
A brazilian developer, Gabriel Menezes Nunes.